Version 3.4.0-3.4.3
# Version 3.4.0-3.4.3
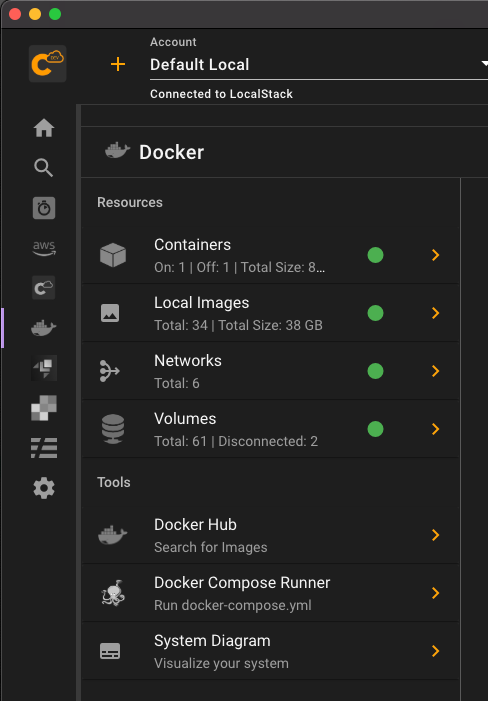
Version 3.4 brought about a unified navigation system. It enables you to easily move through the main parts of the system via a single icon navigation on the left. The breakdown of tools are grouped under Docker, AWS, LocalStack, and a few other high level tools. When drilling into any of the tools, you can then quickly see the main services that are available, and then drill into them. While the file navigation system was an interesting idea for us to be able to see all the connections between services, in the end, it made navigation a bit clunky.
We hope that you find this navigation a bit more satisfactory. Below you can see an example of viewing Docker from the side menu.
# .aws/credentials Management Tool
As we have been working extensively with AWS, we are always modifying our credentials and config files. And with Commandeer, we actually allow you to drive your Commandeer accounts with the files. Meaning that you can use session tokens, assume roles, and other features driven by the files. In order to manipulate this file, we were always jumping back into the finder and a text editor. This is fine for working with one project, but starts to get cumbersome for many.
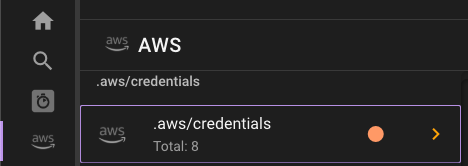
Today, we are excited to announce the ability to manage your credentials directly from Commandeer. You can get to it from the side navigation like so.
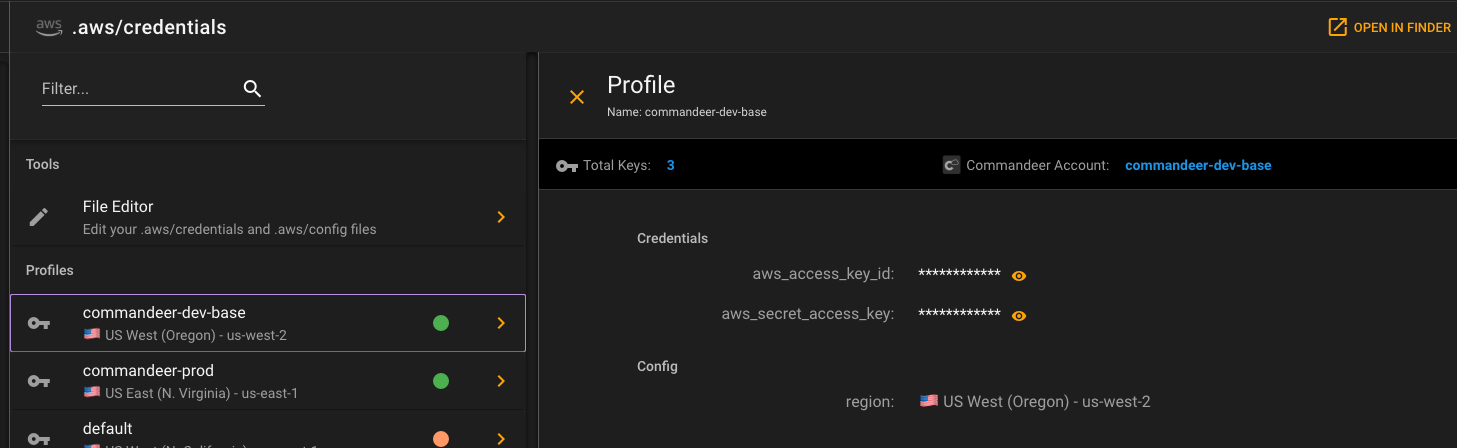
Once there, you can see the full list of your profiles.
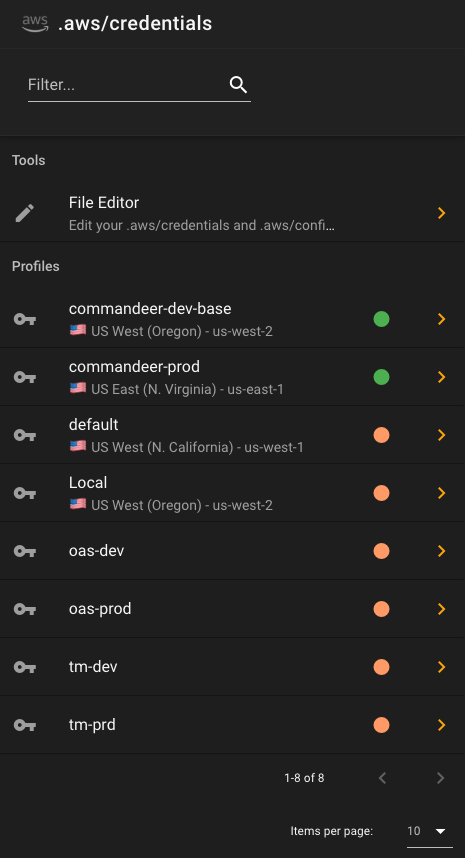
Green means that the profile seems to be configured correctly, and is connected to a Commandeer account. If you see a warning, there are a couple different reasons you might be seeing it.
- A profile in your credentials file does not match one in Commandeer
- There are duplicate profiles in your credentials file that have the same keys
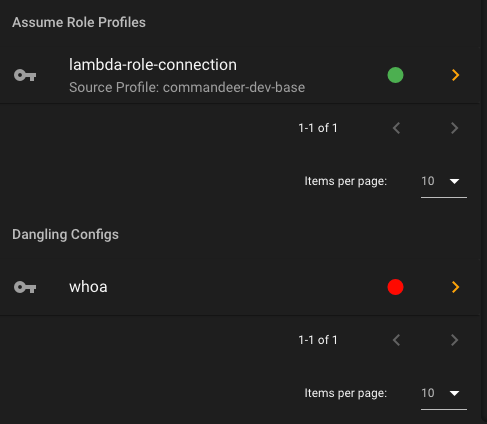
There are also two more sections in the navigation as well.
- Assume Role Profiles - these are assume role setups inside the config file, where a profile has a source_profile and a role_arn, so that when using them, they actually assume a role, and get fresh keys based on the parent keys.
- Dangling Configs - these are profiles in your config file that don't have a corresponding profile in the credentials file.
Clicking into a profile, you can then see a nice breakdown of of the keys associated with it.
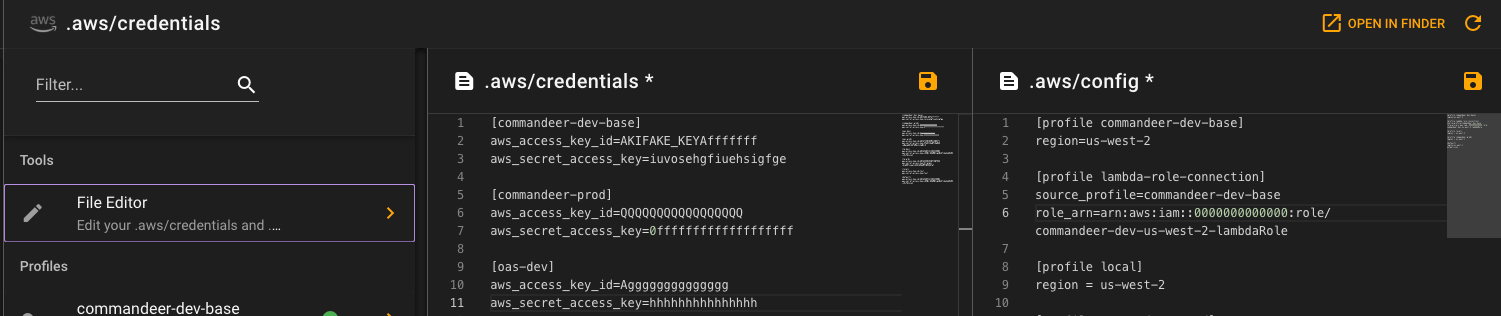
If you want to make edits to the configuration, you can press the File Editor menu item, and edit in a monaco editor.
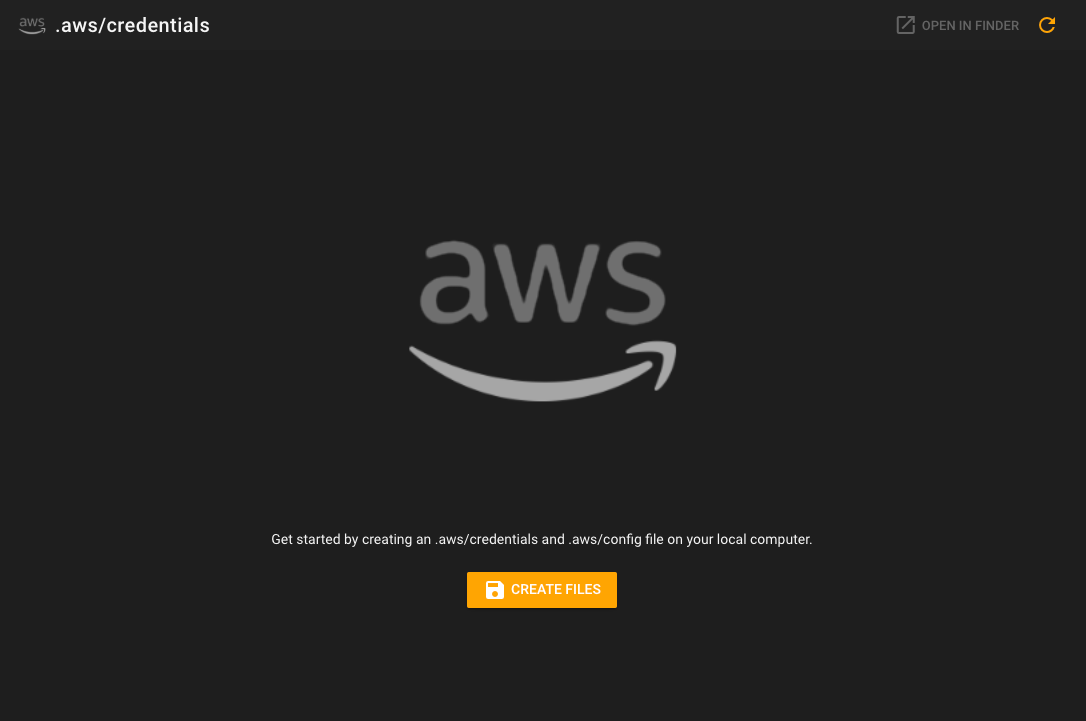
Lastly, if you do not have a credentials and config file setup on your computer. We have that covered too. Go to the credentials page, and we will give you the option of setting one up.
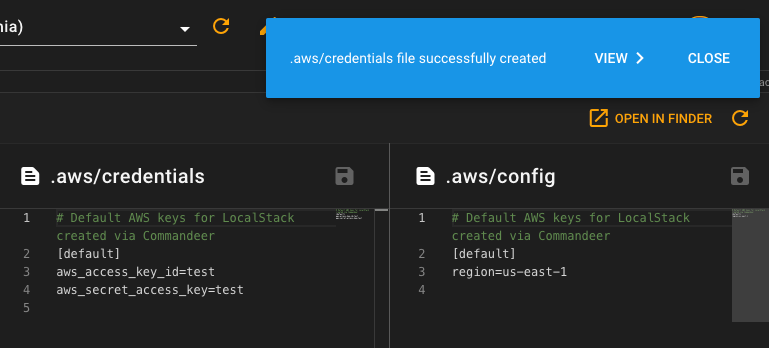
Press the create button, and voila, some files are generated for you in the default location on your computer. You can then always click the 'Open in Finder' button to view them on your computer. But we are hoping you won't need to much anymore!
# Conclusion
We continue to march forward in making your experience using AWS, LocalStack, and Docker as enjoyable as possible. Stay tuned as we continue to add more services and refine features.
